A dedicated bc game download for a compiled bc game app may only be initiated when the binaries are unequivocally and officially provided on the verified main domain. The uncompromising verification of these sources is of existential importance to protect digital assets preventively against sophisticated phishing infrastructures, which pose a highly critical security risk for the bc.game casino when using unregulated third-party downloads.
The Browser Route: How to Use Bc.Game in Germany from Anywhere
The primary and technologically most sophisticated path to using the system architecture on portable devices leads exclusively through the established browser applications of the respective mobile operating systems. To establish a secure, asymmetrically encrypted connection for the bc.game casino deutschland, the preferred browser must be initialized and the exact, cryptographically verified domain must be entered manually into the address bar, as search engine potentials for manipulated indexing (Black Hat SEO) pose inherent risks.
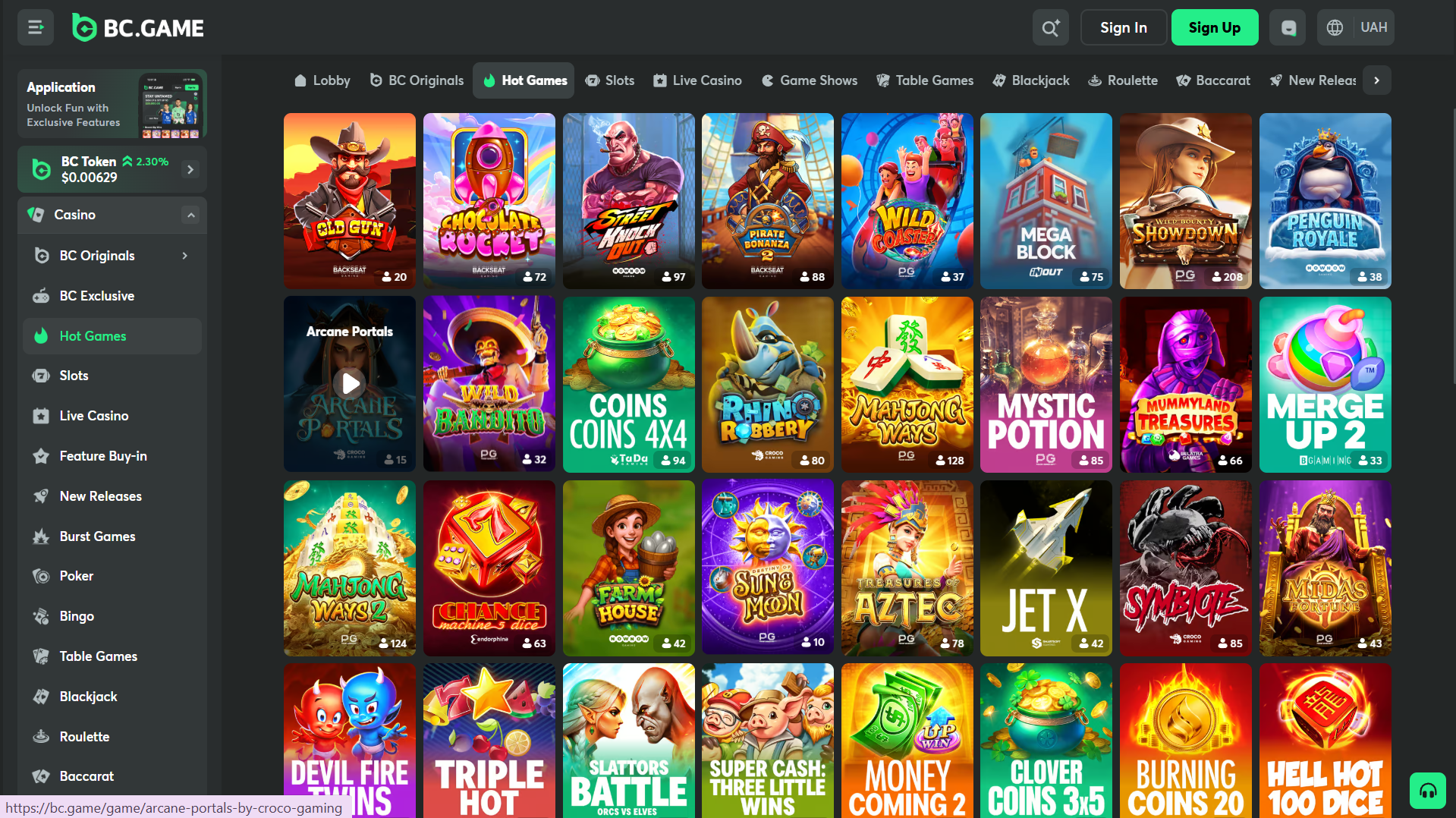
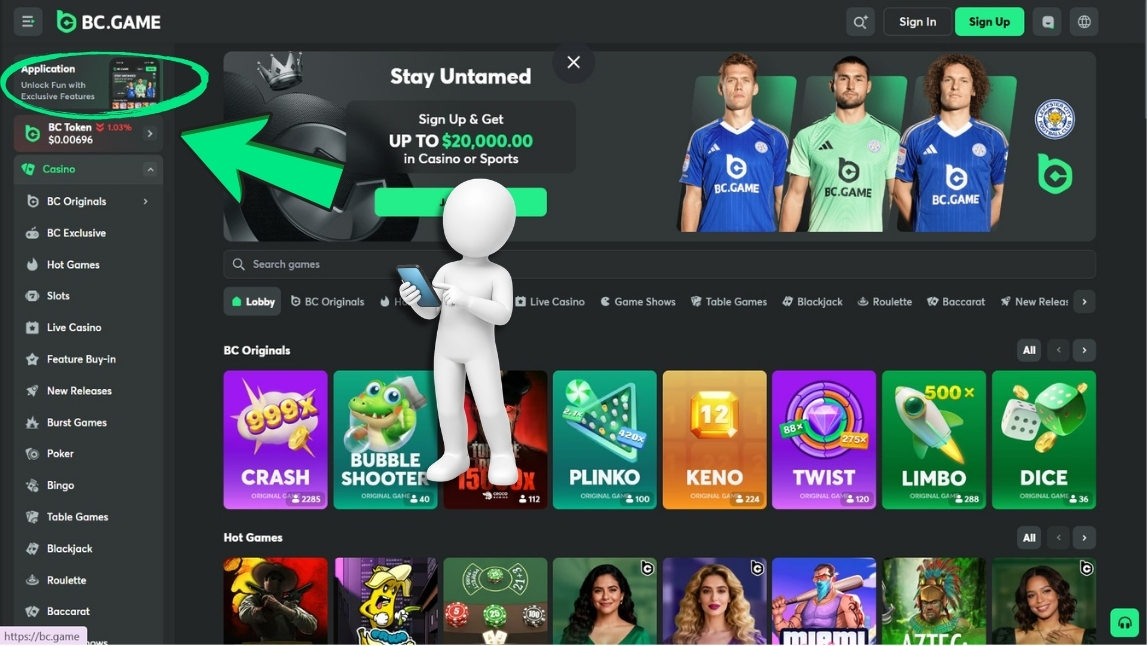
The procedural algorithm of browser-based navigation proceeds in the following strictly defined steps:
- Connection Initialization: Manual entry of the domain bc.game into the mobile browser, followed by verification of the TLS-1.3 certificate via the closed lock symbol in the address bar.
- Cryptographic Authentication: Locating the button for the login process on the rendered user interface and entering the verified credentials or performing the Web3 signature.
- Structural Navigation: After successful validation of the session token, orientation via the dynamically generated main menu (usually a hamburger icon) to the specific sections.
- Module Access: Accessing the areas for the crypto wallet, personal profile, or specific entertainment categories, provided these elements are transmitted and rendered by the frontend server for the current viewport.
This methodical approach guarantees unrestricted, resource-efficient access to all platform functions and represents the absolutely most compatible variant. It operates completely independently of restrictive app store policies and ensures that the client always has access to the latest, server-side patched version of the software. Even highly complex mathematical matrices for bc.game esports betting or dynamic odds for bc game cs2 tournaments are interpreted correctly and without latency by the mobile browser’s rendering engine.
Bc Game Download Detection: Check the Link Before Installation
The methodical verification of potential installation files is the fundamental axiom of applied cybersecurity when dealing with cryptographic interfaces. The system architecture occasionally offers direct installation packages (APKs) for specific operating systems. Validating these files requires a rigorous information technology inspection of the Uniform Resource Locator (URL) before initiating the data transfer.
A legitimate download link is characterized by immutable systemic features: The providing resource must mandatorily be within the official main domain. Any form of unsolicited redirect to different top-level domains or external file hosting services immediately classifies the process as highly security-critical. The Hypertext Transfer Protocol Secure (HTTPS) must be seamlessly implemented across the entire routing path. Furthermore, the visual and textual branding of the download page must be absolutely consistent with the corporate identity of bc games. External sources, unregulated forums, or instant messaging groups distributing executable files or alleged updates operate outside the verified cryptographic certificate space and will, with a probability bordering on certainty, inject malicious code (malware or keyloggers) into the binary structure to read asymmetric keys or authentication tokens. The use of such unverified third-party interfaces systematically leads inevitably to the compromise of the entire decentralized wallet.
Bc Game Download iOS
The guidelines of the Apple App Store regarding the distribution of applications that integrate smart contracts, decentralized financial transactions (DeFi), and stochastic probability algorithms are formulated very restrictively. Due to these infrastructural specifications, in empirical practice there is often no regular bc game download ios in the form of a native .ipa file via the centralized Apple ecosystem.
If the graphical user interface of the official platform does not provide an explicit installation routine certified by Apple or a corresponding profile instruction, the only alternative information technology imperative is: Access must occur exclusively via the mobile Safari browser or by creating a Progressive Web App (PWA). The PWA method extracts the web manifest of the site and generates an isolated, app-like full-screen environment on the home screen without violating the operating system’s security architecture (sandboxing). The conscious search for unofficial iOS builds or the installation of so-called Mobile Device Management (MDM) profiles from unregulated sources represents a blatant security risk. Such external profiles often grant the provider deep administrative kernel-level rights on the end device, whereby all encrypted data traffic, including all passwords and Web3 signatures, can be intercepted and redirected to hostile servers.
Quickly Solving Mobile Problems: Cache, Network, and Blockers
The empirical analysis of server logs and client error messages shows that temporary access anomalies, incorrect renderings of the Document Object Model, or rejected API requests during mobile use are mostly due to local misconfigurations or asynchronous data states on the end device. These software-based complications can be efficiently diagnosed and resolved through methodical troubleshooting.
The universal solution approaches include the following procedural interventions:
- Invalidation of local storage: Physically deleting the browser cache and temporary website data (cookies) forces the download of the current, uncorrupted JavaScript libraries from the bc gaming servers upon the next page visit.
- Browser switch: Temporarily switching to an alternative, standardized rendering engine (for example, from Safari to Chrome) can isolate compatibility issues caused by specific, restrictive engine updates.
- Disabling interfering scripts: Strict ad blockers or privacy extensions often mistakenly classify legitimate WebSockets or RPC (Remote Procedure Call) calls as tracking attempts and block communication; these must be temporarily disabled for the duration of use.
- Time synchronization: An incorrect system time on the smartphone leads to the immediate invalidation of asymmetric SSL certificates (Time-of-Check to Time-of-Use algorithms) and TOTP codes; activating the Network Time Protocol (NTP) in the device settings is mandatory.
- Network stability: Ensuring a stable, packet-loss-free TCP/IP connection is essential, as asynchronous communication interruptions during the transmission of bet hashes can lead to procedural evaluation conflicts.

Data Protection on the Go: Quick Security Check
The inherent mobility of use on smartphones entails significantly altered and often more critical attack vectors for potential security compromises of the digital identity. When interaction with the platform’s complex algorithms takes place in public spaces or shared network infrastructures, the strict and uncompromising adherence to cryptographic and operational hygiene is of existential importance for maintaining data protection.

An essential parameter is the absolute avoidance of the device-side function for automatically saving access data in the browser, unless the end device is secured by strong biometric factors (FaceID or fingerprint sensors) at the hardware level. The use of unencrypted, public Wi-Fi hotspots in urban areas opens up significant attack surfaces for man-in-the-middle attacks (for example, through ARP spoofing), where malicious actors can intercept data traffic. Using a Virtual Private Network (VPN) encrypts the tunnel, but must always be used with respect to the platform’s guidelines and without the explicit goal of circumventing regional geo-blockades (geo-spoofing). Regarding session management, the scientific maxim applies that after ending the interaction, an active, manual logout must occur via the user interface menu. Simply closing the browser tab usually leaves the session cookie in an active state, which, in the event of physical loss of the device, enables immediate full access to the crypto wallet, even if a regular bc game no deposit bonus or complex deposit bonuses were accumulated beforehand.